by Peter Kieseberg, Simon Tjoa and Herfried Geyer (St. Pölten University of Applied Sciences)
Blockchains offer a valuable set of tools to provide resilient distributed solutions for applications that require a high level of integrity. Still, apart from being used to store cryptocurrency data, blockchains are not used in many other areas. This article gives an overview of the major obstacles to the uptake of blockchains, from an information security perspective.
Security management is one of the most important parts of any resilient security strategy for real-life systems. A defender must be able to detect incidents, act coherently and according to best practices, and to learn from attackers in order to develop mitigation strategies for the future.
Several standards and best practices have been devised; the best known of which is arguably the ISO27k family [1]. Standardisation is a particularly important process in security management, not only to address technical issues like compatibility with other organisations, but also as an insurance for the decision-makers within those companies, for when large breaches occur.
Blockchains as ledgers for cryptographic currencies currently exist in a rather special environment, since through their development and the original stakeholders, they typically do not have to adhere to the same levels of accountability and privacy that traditional IT systems do. This approach may work for a system that exists outside of the traditional financial mechanisms, but the scenario is different in the traditional IT landscape, like banking or land registers. In these environments, the inherent risks of this more “free” approach will not be accepted by typical end-users, or even be illegal. Some experts believe that a major reason for the slow acceptance of novel blockchain applications outside the purely speculative area of cryptocurrencies is that trust, accountability and thorough control over the data on the chain are currently unavailable for blockchain mechanisms [2].
One major problem when introducing blockchain-based systems is that they are usually treated in the same way as any other form of IT system with respect to security management. However, they possess several features that differ fundamentally, depending on the exact type of blockchain (e.g., public vs. private, type of consensus mechanism), as well as the implementation (see Figure 1). One major difference is the highly distributed nature of the systems, which is otherwise generally restricted to niche applications or highly unregulated applications like file sharing and bit torrent. Furthermore, unlike most other applications, blockchain-based systems lack a mechanism to remove data from the chain; on the contrary, most blockchain systems do not support the deletion of data at all. This is in stark contrast to most filesharing applications, where data is rendered inaccessible after a while, depending on the interest of the other participants, and at some point, typically dwindles into obscurity. In blockchain applications on the other hand we must assume that the attacker might be in possession of any arbitrary selection of old versions of the chain, including all its content. This is especially important when considering the issue of access control. When it comes to providing cryptographic access control, unlike in normal distributed systems it is not possible to update protection by re-encrypting all data on the chain, as the attacker can always be in the possession of old versions.
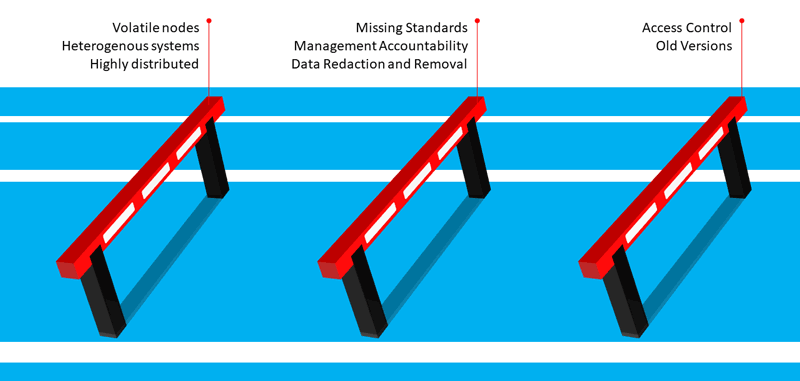
Figure 1: Key security management concerns in the blockchain ecosystem.
Another trust-related problem, for which a solution would be a key to the widespread adoption of blockchains, is the issue of redaction of wrong information entered into the chain. While there already exist methods for marking this information as invalid, it cannot be removed altogether from the chain. This is especially important when illegal content like child pornography is introduced into a chain, where full and un-recoverable deletion is required. While there are solutions to this problem, they typically do not remove the illegal data from the chain but merely render it inaccessible. Managing the system as a responsible entity thus can even result in legal problems. Furthermore, the nature of these distributed systems is highly volatile, with nodes entering and leaving, new nodes being introduced and old ones never operating again. This makes asset management very complex, especially since it is unclear to the system provider, which nodes work together, or might belong to the same entities.
Last, but not least, another key issue from a security management perspective is heterogeneous systems: Most companies already run traditional IT systems and won’t change all of it to blockchains at once, which means that blockchain-based systems need to interface with traditional programs that use totally different approaches for deciding when a transaction is valid, how data is stored and access managed. Thus, these interfaces would pose an important attack surface, especially since there are currently no standardised solutions to securely integrate arbitrary blockchains into complex traditional systems [3].
Security management is a major issue in IT security, as many practical problems in securing complex environments cannot be reduced to pure technical issues. Furthermore, technical solutions are often rendered useless because it is impossible to introduce them to the system. Security management is thus one of the most important aspects in security, and given the complexity and special requirements of blockchains, novel approaches are required.
In the JRC for Blockchain Technologies and Security Management [L1], we tackle these issues and provide best practices for adopting blockchain-based systems in addition to traditional IT systems. Our focus is on the issues of trust and access control, but we also provide best practices for dealing with illegal content from the design phase onwards. Furthermore, we provide insights into how to adopt standards from the ISO27k family as applied to the particularities of blockchain-based systems.
Link:
[L1] https://research.fhstp.ac.at/projekte/josef-ressel-zentrum-fuer-blockchain-technologien-sicherheitsmanagement
References:
[1] ISO/IEC 27001:2017. Information Technology - Security Techniques – Information Security Management Systems – Requirements.
[2] L. König, et al.: “The Risks of the Blockchain A Review on Current Vulnerabilities and Attacks. J. Internet Serv. Inf. Secur., 10, 110–127, 2020.
[3] L. König, et al.: “Comparing Blockchain Standards and Recommendations. Future Internet, 12(12), p.222, 2020.
Please contact:
Peter Kieseberg
St. Pölten University of Applied Sciences, Austria