by Georgios M. Nikolopoulos (IESL-FORTH, Greece)
Quantum cryptography is the science of exploiting fundamental effects and principles of quantum physics, in the development of cryptographic protocols that are secure against the most malicious adversaries allowed by the laws of physics, the “quantum adversaries”. So far, quantum cryptography has been mainly identified with the development of protocols for the distribution of a secret truly random key between two legitimate users, known as quantum key-distribution (QKD) protocols. Beyond QKD, quantum cryptography remains a largely unexplored area. One of the main ongoing projects at the Quantum Optics and Technology group of IESL-FORTH [L1], is the design and development of cryptographic solutions, which rely on fundamental quantum-optical systems and processes, and offer security against quantum adversaries.
Electronic communications and transactions constitute one of the main pillars of our society. The role of cryptography is to ensure the stability of this pillar, by providing techniques for keeping information secure, for determining whether information has been maliciously altered, and for determining who authored pieces of information. To a large extent, modern public-key cryptography relies on mathematical problems, such as the factorisation of large integers and the discrete logarithm problem, which are considered to be hard to solve on classical computers, in the sense that there are no known efficient classical algorithms for solving these problems for all integers in polynomial time. Given, however, that the non-existence of such algorithms has never been rigorously proved, most of the widely used public-key cryptosystems are susceptible to advances in algorithms or in hardware (computing power). Indeed, Peter Shor has proved that a quantum computer could solve both of the aforementioned mathematical problems efficiently.
Though a fully functional universal quantum computer of the necessary size to break widely used cryptosystems is still far off in the future, there is a necessity for ensuring the security, the integrity and the authenticity of data that is encrypted or digitally signed today, and they have long lifetime. Unfortunately, the currently available QKD systems become inefficient for large networks (many users), where the establishment of many pairwise secret keys is needed, and the key management remains a major problem. Moreover, QKD alone does not address many other cryptographic tasks and functions, which are of vital importance in everyday life (e.g., authentication, non-repudiation, integrity, etc.).
Cryptographic research in our theoretical group started in 2007, and its emphasis is on the design and the development of quantum cryptographic primitives and protocols, which rely on fundamental quantum-optical systems and processes, and offer security against quantum adversaries [1-3]. Typical quantum-optical systems are single photons, light in various quantum states, atoms, waveguides, and cavities. A description of our activities and related publications can be found at [L1] and [L2].
Entity authentication (identification) is an important cryptographic task, in which one party (the verifier) obtains assurance that the identity of another party (the claimant) is as declared, thereby preventing impersonation. Most of the entity authentication protocols (EAPs) used for everyday tasks (e.g., transactions in automatic teller machines), rely on dynamic challenge-response mechanisms, which combine something that the claimant knows (e.g., a PIN), with something that the claimant possesses (e.g., a smart card). In such mechanisms, after the user types in the correct PIN, the smart card is challenged with random numerical challenges, and the verifier checks if the responses of the card are valid. Conventional EAPs are not totally immune to card-cloning, while they are susceptible to emulation attacks, in which an adversary knows the challenge-response properties of the smart card (e.g., by hacking the database of challenge-response pairs), and his task is to intercept each numerical challenge during the verification stage, and send to the verifier the expected response.
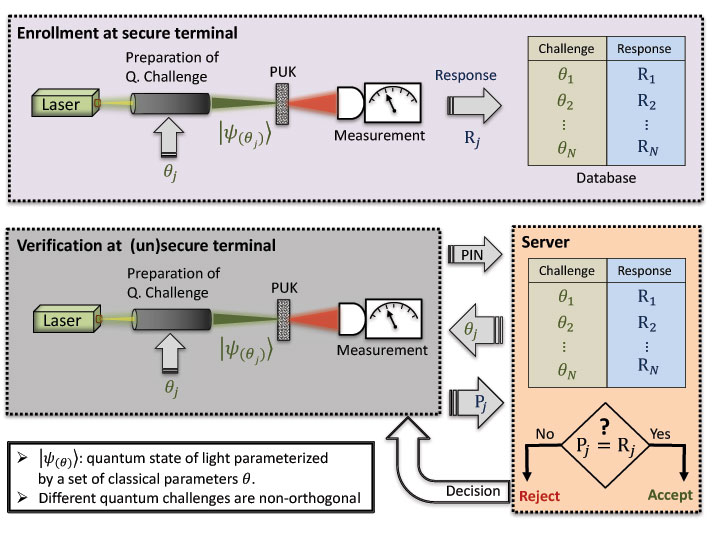
Figure 1: Schematic representation of a quantum-optical EAP, which relies on a challenge-response mechanism. The enrolment stage is performed once by the manufacturer, while the verification stage takes place each time the holder of the PUK has to be authenticated.
Currently, optical physical unclonable keys (PUKs) are considered to be the most promising candidates for the development of highly secure EAPs. Such PUKs are materialised by an optical multiple-scattering disordered medium, and they are considered to be unclonable, in the sense that their cloning requires the exact positioning (on a nanometre scale) of millions of scatterers with the exact size and shape, which is considered to be a formidable challenge not only for current, but for future technologies as well. Typically, a PUK-based EAP relies on a challenge-response mechanism, in which the PUK is interrogated by light pulses with randomly chosen parameters, and acceptance or rejection of the PUK is decided upon whether the recorded responses agree with the expected ones. Although, in general, PUK-based EAPs are more robust against cloning than conventional EAPs, they are still vulnerable to emulation attacks when challenges pertain to classical light, and the verification set-up is not tamper-resistant. To eliminate this vulnerability, in collaboration with E. Diamanti (CNRS, Université Pierre et Marie Curie), we have proposed a novel quantum-optical EAP in which a PUK is interrogated by randomly chosen non-orthogonal coherent quantum states of light (see Figure 1) [1]. The response of the PUK to a quantum state (challenge) is sensitive to the internal disorder of the PUK, which makes our protocol collision resistant, and robust against cloning. Moreover, on-going research shows that the security of our protocol against an emulation attack relies on the laws of quantum physics, which do not allow unambiguous discrimination between non-orthogonal quantum states, while information gain cannot be obtained without disturbing the quantum state under interrogation. The proposed protocol can be implemented with current technology, and its performance under realistic conditions is the subject of future theoretical and experimental work.
Links:
[L1] http://www.quantum-technology.gr/
[L2] http://gate.iesl.forth.gr/~nikolg
References:
[1] G. M. Nikolopoulos, E. Diamanti: “Continuous-variable quantum authentication of physical unclonable keys”, Scientific Reports, 2017, 7, p. 46047.
[2] G. M. Nikolopoulos, T. Brougham: “Decision and function problems based on boson sampling”, Physical Review A, 2016, 94, p. 012315.
[3] G.M. Nikolopoulos: “Applications of single-qubit rotations in quantum public-key cryptography”, Physical Review A, 2008, 77, p. 032348.
Please contact:
Georgios M. Nikolopoulos
IESL-FORTH, Greece