by Georg Merzdovnik, Damjan Buhov, Artemios G. Voyiatzis and Edgar Weippl (SBA Research)
Protecting user security and privacy on the internet takes more than transport layer security (TLS) and strong cryptographic algorithms: utilizing TLS notary services and certificate pinning for improved defences against prevalent third-party tracking.
Smartphones and mobile devices are becoming an integral part of life in the connected world. They allow easy access to information and content generation as well as consumption. A significant driving factor for their wide acceptance is the enormous number of available applications (commonly referred to as ‘apps’). For example, by the beginning of 2017, the Google Play Store offered more than 2.6 million apps for smartphones, ranging from games and weather apps to office suites and banking apps. While these applications offer huge potential, they can also, either intentionally or inadvertently, pose a security and privacy risk to their users.
At the Josef Ressel Centre for User-friendly Secure Mobile Environments (u'smile) we are analysing security issues in current and future mobile applications. We are working on: (i) the design, development, and evaluation of concepts, methods, protocols, and prototype implementations for addressing security risks, and (ii) communication and co-ordination with industry partners and standardisation organisations with the goal of establishing globally accepted standards for secure, interoperable mobile services.
One area that we are working on is the security and privacy of network communications of mobile apps and their cloud-based services. All published applications go through inspection for malware behaviour before being published in the Google Play Store. However, user tracking and other forms of privacy leaks are still feasible, especially through advertisements included in apps and web applications to provide a revenue stream for the developers of free or low-priced software. A large number of tracker-blocking applications and apps are available for privacy-conscious users. We performed a large-scale study of the effectiveness of available tracker-blocking tools [1], which showed that despite their sophistication, tools cannot defend against all privacy leaks. Furthermore, a significant portion of applications transmit information over HTTP without establishing a secure connection over the TLS protocol (i.e., use HTTPS). This bad practice allows traffic interception and content inspection in-transit, increasing the threat of user tracking.
Digital certificates are used by TLS and allow verification of the identity of the server an app is connecting to as well as setting up a connection for exchanging information securely. Numerous certificate authorities come pre-installed in modern mobile operating systems, all of which are equally trusted by an app to offer a valid certificate for any internet server. TLS notary services collect and distribute information from TLS certificates presented at various points on the internet. Upon connecting over HTTPS to a website, an app can consult a TLS notary service and check if the presented certificate is the same as the one presented to other users. If not, it might be a good indicator that the connection with the server has been intercepted and a fake-but-valid certificate presented to the user for nefarious purposes (i.e., a man-in-the-middle attack). We performed a longitudinal study of openly-accessible TLS notary services spanning one year [2]. Our findings indicate that while the offered service is indeed valuable for internet hygiene, there is currently little incentive for service operators to cover the incurred costs and thus, their availability is dropping.
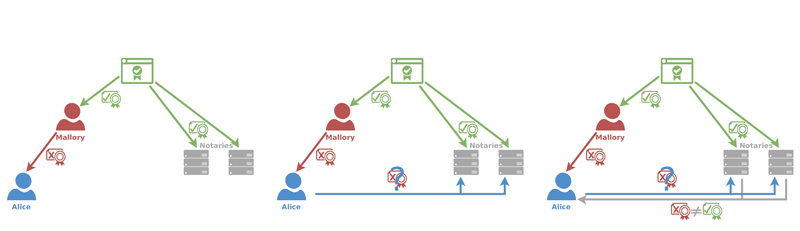
Figure 1: Example of TLS notary service operation – the connection to the server is only trusted if the two certificates match.
‘Certificate pinning’ is an approach used by highly-sensitive apps (e.g., banking apps) to ensure that only selected, app-specific certificates are used to validate server identity. However, developers often fail to implement certificate pinning correctly. In some cases, this even breaks the normal TLS certificate validation procedure, rendering the app more insecure compared to not implementing certificate pinning at all. We designed, implemented, and demonstrated a system-level approach that transparently forces certificate pinning for installed apps and thus, reduces their exposure to related attacks [3]. Our approach does not require developers to update their app. As a next step, we extended our design towards a notary-assisted approach. This allows proper certificate pinning even when the application is connecting with a web resource for the first time by relying on the collective knowledge already contributed to the TLS notary services. Also, the new design requires minimal if any intervention by users; users are effectively freed from any uninformed system-level security decisions, which are otherwise a common source of security problems.
Secure mobile environments are key building blocks for the Internet of Things (IoT) world. The need for security is becoming increasingly apparent as self-managing mobile devices and apps are deployed and operate transparently to the users. Researchers at u’smile have been working on this topic since October 2012. The Josef Ressel Center u’smile is funded by: the Christian Doppler Gesellschaft (CDG); A1 Telekom Austria AG; Drei-Banken-EDV GmbH; LG Nexera Business Solutions AG; NXP Semiconductors Austria GmbH; and Österreichische Staatsdruckerei GmbH.
Links:
[L1] https://usmile.at/
[L2] https://www.sba-research.org/
References:
[1] G. Merzdovnik et al.: “Block Me If You Can: A Large-Scale Study of Tracker-Blocking Tools”, in 2nd IEEE European Symposium on Security and Privacy (IEEE Euro S&P), 2017.
[2] G. Merzdovnik et al.: “Whom you gonna trust? A longitudinal study on TLS notary services”, IFIP DBSec 2016.
[3] D. Buhov, et al.: “Pin It! Improving Android network security at runtime”, IFIP Networking 2016.
Please contact:
Georg Merzdovnik and Edgar Weippl
SBA Research, Vienna, Austria