by Zeeshan Ali Khan and Peter Herrmann (NTNU)
In our daily lives, we are surrounded by a plethora of connected devices. But can we be sure that they are all secure and will not start malicious attacks against us? Many devices are small and have only limited processing and battery power such that traditional security mechanisms cannot be used. In this article, we propose a trust-based intrusion detection system that is resource-friendly and offers energy-efficient media access.
Innovative technology plays an increasingly important role in our daily lives. We deal not only with independent devices, but with devices that communicate with each other and form an Internet of Things (IoT). According to most predictions, several billions of ‘things’ will be connected with the internet in the coming years [L1]. Many of these connected devices will be very small and cheap such that they can be placed wherever they are required. The interconnectedness of the IoT devices and networks, however, poses a significant risk since the systems will be subject to malicious attacks. An example is denial of service attacks precluding the devices from communicating with other stations. Therefore, security issues must be considered for the engineering and deployment of IoT networks. Further, the applied security mechanisms have to address the limitations of many devices in terms of memory, power, and bandwidth. Otherwise, the devices can be quickly depleted.
In the scope of an ERCIM fellowship, we propose the use of Intrusion Detection Systems (IDS) to minimise the chances of Denial of Service (DoS) attacks. Our solution concentrates on attacks that actively try to omit crucial communication between nodes. In ad-hoc networks, this can occur via insider attacks in which the intruder manages to compromise the routing capability of devices. To reduce the computing effort for the small devices, we use trust management [1] which allows the emulation of trust relations in other entities by relatively lightweight but powerful mechanisms. In a computer, one can describe the trust of an entity in another one by a trust value. Using special metrics, the trust values can be adapted based on the good and bad experiences one has with a trustee over time. This reflects the development of trust relations in quite a natural way. Moreover, operators exist that allow us to consider recommendations by third parties and to aggregate the trust values of several entities with a trustee to a more general reputation.
In [2], we introduced a trust-based IDS for the popular Routing Protocol for Low power and Lossy networks (RPL [L2]). An example of RPL based IoT network for Healthcare applications is explained in Figure 1. In this approach, network nodes monitor the behaviour of adjacent nodes, e.g., by listening to whether they forward messages as demanded by the protocol. When a node forwards a message correctly within a certain period of time, this counts as a positive experience and otherwise as a negative one. Based on that, the personal trust values are amended and, by exchanging them with other nodes, a more general reputation of a node is built. If the trust-building process reveals that a certain node has a bad reputation among its neighbours, it is assumed to be infected and can be quarantined.
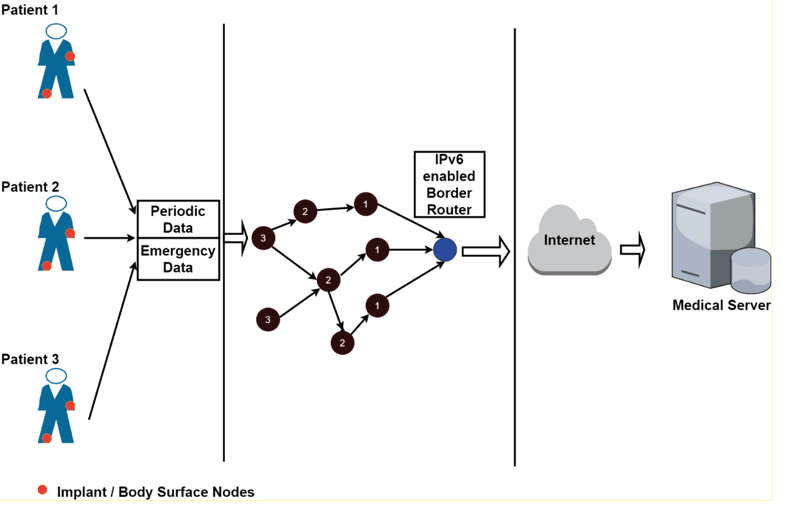
Figure 1: An Example of RPL based IoT network, for Healthcare Application.
To get practical evidence of our approach, we are in the process to create a test-bed consisting of Z1 devices running the operating system Contiki. First results show that the computations needed to build trust values are not computing intensive. On the other side, however, the trust based mechanisms seem to drain the often scarce battery supplies of a node. The main reason for that is that the monitoring of the neighbouring nodes is achieved by active channel listening, i.e., by constantly listening to the wireless network channel which is an energy intensive activity.
To overcome this problem, we have extended our work and propose to use our approach to the media access protocol IEEE 802.15.4 [L3] that offers mechanisms to reduce active channel listening. A first outcome of this extension is that a beacon-based mode with guaranteed time slots, offered by this protocol, can reduce the active channel listening dramatically. Our simulations and analysis showed that the reduction will be between 50 % and 75 %. Like with the RPL protocol, the extension shall be further tested with our Z1-based test-bed.
Finally, we are in the process of developing a study reviewing the state of the art of IDS existing for the IoT networks. Here, we will also look on existing systems for Mobile Ad-hoc Networks (MANET), Wireless Sensor Networks (WSN) and Cyber Physical Systems (CPS) that have properties close to IoT and might also be usable in this area.
Links:
[L1] http://www.woodsidecap.com/wp-content/uploads/2015/03/WCP-IOT-M_and_A-REPORT-2015-3.pdf
[L2] https://tools.ietf.org/html/rfc6550
[L3] http://www.ieee802.org/15/pub/TG4.html
References:
[1] A. Jøsang: “A Logic for Uncertain Probabilities”, International Journal of Uncertainty, Fuzziness and Knowledge-based Systems, vol. 9, pp. 279-311, 2001.
[2] Z. A. Khan, P. Herrmann: “A Trust Based Distributed Intrusion Detection Mechanism for Internet of Things”, in 31st IEEE International Conference on Advanced Information Networking and Applications (AINA), Taipei, Taiwan, 2017.
[3] G. Swamynathan, K. C. Almeroth, B. Y. Zhao: “The design of a reliable reputation system”, Electronic Commerce Research, vol. 10, no. 3, pp. 239-270, 2010.
Please contact:
Zeeshan Ali Khan, Peter Herrmann
NTNU Trondheim, Norway.