by Matthias Wenzl (Technikum Wien), Georg Merzdovnik (SBA Research) and Edgar Weippl (SBA Research)
The vast majority of the IoT is made up of computing devices that are highly specialised for their particular purpose. Owing to their specialisation and the resulting constraints, such as energy consumption and the deterministic fulfilment of deadlines (real-time requirements), these embedded systems tend not to share many security features in common with standard operating systems. We aim to provide automated approaches to implant security features into connected embedded systems to counter the lack of security features in the backbone of the IoT and improve their resilience against unauthorised access attempts.
The Internet of Things (IoT) is formed by an ever-growing number of interconnected embedded systems. An embedded system is a computing device designed for a specific purpose that operates under certain constraints (e.g., hardware and software tightly intertwined to monitor traffic conditions on a motorway). Use-cases like smart cities, Industry 4.0, Car2X communication and ambient assistive technologies promote networked embedded devices to become ubiquitous companions in our daily lives. Unfortunately, many of the computing devices in the IoT lack even the simplest form of security features, resulting in numerous successful attacks on IoT devices in recent years. Security features, specifically exploit mitigations, are procedures that reduce the likelihood of an unpatched software vulnerability being exploited by an adversary in such a way that it is possible to mislead the system to do unintended operations (e.g., address space layout randomisation (ASLR) that is built into every Microsoft Windows operating system derivate since Windows Vista (2007), as well as enabled by default in OpenBSD since 2003 and Linux since 2005). The lack of security features in embedded systems is primarily based on application specific constraints, hardware requirements (physical size, energy consumption, real-time requirements [1]), software diversity (full features OS like Linux, *BSD, Windows IoT Core, real-time OS like FreeRTOS, no OS at all) and security agnostic design decisions (e.g. unreflected usage of legacy code).
Well-known security features such as address space layout randomisation (ASLR), non-executable pages and stack layout transformation (SLX) are readily available for general-purpose operating systems. However, according to a study presented in 2017 [2], not all variants of general-purpose operating systems deployed to embedded computing platforms are configured to utilise security features. Additionally, many embedded operating systems lack these kinds of features altogether. This is primarily caused by the fact that many embedded operating systems aim to support a wide variety of target hardware, including even the smallest devices. For example, the widely used FreeRTOS supports target platforms ranging from Microchip’s SAMD20 microcontroller with 16 kB non-volatile and 2 kB volatile memory to full featured IA-32 based systems. Consequently, support for inherent security features is omitted. Additionally, almost all security features introduced at an operating system level protect either every component of interest (e.g., function entry point) or none. This leads to an increase in resource consumption in terms of memory and runtime that might not be practicable (e.g., the implementation of a shadow-stack at an operating system level doubles the amount of used stack memory in terms of return addresses). Nevertheless, patching all available embedded operating systems and already circulating legacy systems at source level is clearly illusive owing to their large heterogeneity.
Therefore, the aim of the FFG-funded project ISaFe [L1] is to provide automated approaches to implant security features into connected embedded systems to counter the lack of security features in the backbone of the IoT starting with September 2019. Together with the IoT startup Riddle & Code, whose aim is to provide an interface between embedded systems and blockchain technology, SBA-Research and the FH Technikum Wien, all situated in Vienna, Austria, pursue a novel approach based on binary rewriting to retrofit already existing IoT systems in order to make them more resilient against unauthorised access attempts.
Binary rewriting describes the alteration of a compiled and possibly (dynamically) linked program without having the source code at hand in such a way that the binary under investigation stays executable [3]. In the context of hardening this means to implant security features into the binary under investigation.
Unfortunately, constraints such as real-time requirements, or memory constraints are very common in embedded systems software. Thus, a straightforward approach like applying binary rewriting for hardening purposes on every point of interest (e.g., every function call, every branch) in a binary with constraints is not feasible due to the introduction of possible constraint violations. At the core, our approach requires us to solve an optimisation problem that maximises the number of protected vulnerable spots (locations within the firmware of interest that might be subject to attack, which we attempt to identify via taint tracking) with the most efficient security features, at the lowest possible costs - in terms of memory and run time overhead - while obeying the system’s constraints. The overall idea if the presented approach can be seen in Figure. 1.
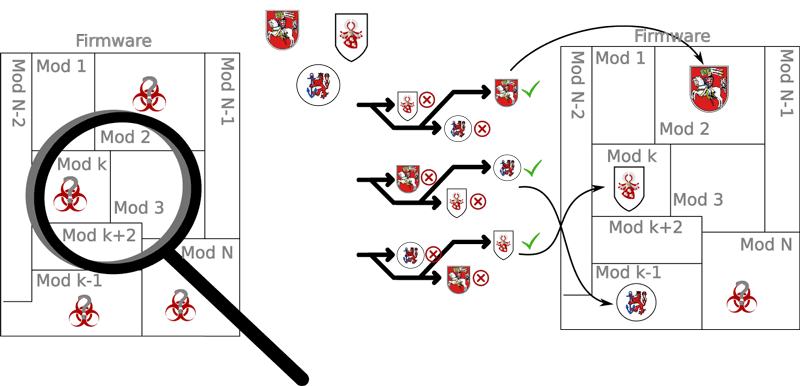
Figure 1:The core idea of project ISaFe read from left to right - Find locations within a firmware image that utilises data from external inputs in certain ways. Then choose and implant selected security features to mitigate possible attacks on the detected locations in such a way that as much as possible of the detected locations are protected and the firmware under investigations still adheres to its constraints (real-time, memory consumption, etc).
Link:
[L1] https://kwz.me/hEB
References:
[1] H. Kopetz: “Real-Time Systems: Design Principles for Distributed Embedded Applications”, second edition, Springer, 2011.
[2] J. Wetzels: “Ghost in the Machine: Challenges in Embedded Binary Security”, Usenix Enigma, 2017. https://www.usenix.org/conference/enigma2017/conference-program/presentation/wetzels
[3] M. Wenzl, et al.: “From Hack to Elaborate Technique - A Survey on Binary Rewriting”, 2019, https://doi.org/10.1145/3316415
Please contact:
Matthias Wenzl
Technikum Wien, Austria
Georg Merzdovnik and Edgar Weippl
SBA Research, Austria