by Christian Kudera, Georg Merzdovnik and Edgar Weippl (SBA Research)
The heterogeneous landscape of IoT devices poses new challenges to the deployment of honeypots. So far no generic honeypot framework exists that is capable of attracting attacks for the wide variety of hardware and software architectures. By combining real world device information and virtualisation techniques, we aim to build AutoHoney(I)IoT, a framework that automatically creates target device tailored honeypots for the (Industrial) Internet of Things, which are capable of convincing attackers that they are breaching a real device instead of a decoy.
The interconnection of physical devices, vehicles, household appliances and other objects with electronics, software, sensors and actuators has become an integral part of our modern lives. The industrial sector is also undergoing a change in device communication. Traditionally, automated factories and critical infrastructure were strictly separated from the Internet. However, since the advent of Industry 4.0, devices at control as well as supervisor level are frequently connected to the Internet to collect analytic data. The resulting network is called the “Internet of Things” (IoT) and “Industrial Internet of Things” (IIoT). Attackers seek to compromise such interconnected devices with malware campaigns [1, 2] to use them for spam distribution, Distributed Denial of Service (DDoS) attacks, cryptomining, or as an attack vector in Advanced Persistent Threat (APT) attacks. For this reason, interconnected devices are exposed to continuous threats and ongoing attacks. The large set of diverse hardware and software combined with the neglection of security best practices, such as the use of the same default credentials on all devices, the often non-existent update policies, and the lack of software hardening techniques render IoT and IIoT devices an ideal target for attackers. Many solutions have been proposed to monitor the Internet for malware infections. “Honeypots” are a common practice but owing to the heterogeneity of the devices they are substantially harder to implement in the IoT and IIoT domain than in the field of commodity systems (e.g., desktop computers, smartphones). The heterogeneous landscape of IoT and IIoT devices poses new challenges to the deployment of honeypots.
The goal of the research project AutoHoney(I)IoT [L1] is to provide a framework that automatically creates target device tailored honeypots for the (Industrial) Internet of Things, which are capable of convincing adversaries that they are breaching a real device instead of a decoy. The honeypots will be executed in an emulation environment that is able to interact with the outside world over common IoT and IIoT communication channels and allows fine-grained supervision techniques to be applied to monitor an adversary’s behaviour throughout his entire attack. Figure 1 illustrates the overall concept of the AutoHoney(I)IoT framework. As input, the framework requires the firmware of the device to be virtualised as well as a database containing real world device information of common microcontrollers and system on a chips (SoCs). The framework’s intended functionality is to analyse a firmware dump and find a Qemu [3] appliance capable of executing the firmware. Furthermore, external peripherals (e.g., network access) are attached as needed.
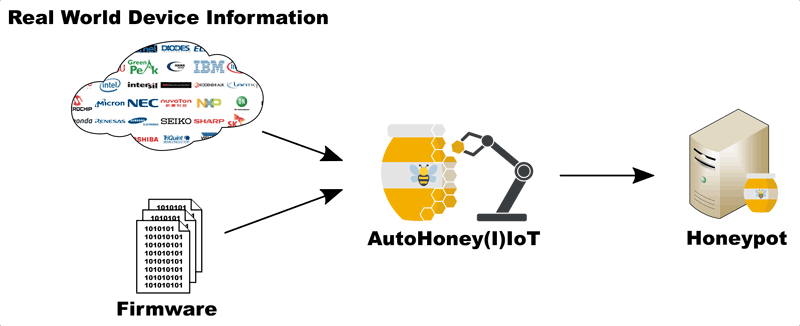
Figure 1: Overview of the AutoHoney(I)IoT framework.
The analysis is based on a two-step approach. The aim of the first step is to detect the architecture (e.g., ARM, MIPS, PowerPC, x86) of the firmware. The main idea of the second step is to apply fine-grained supervision techniques during the execution to identify the most appropriate processor. Therefore, the firmware is executed first on a generic processor corresponding to the identified architecture. Most likely this will result in an instruction mismatch, memory mismatch or internal peripheral mismatch, since there is a plethora of different embedded processors from various vendors with a wide variety of technical characteristics (e.g., central processing unit types, memory maps). During the emulation an algorithm attempts to identify an admissible embedded processor that is capable of executing the firmware dump. For this purpose, we create a database containing the real world technical characteristics of microcontrollers and SoCs from various vendors. The execution and fine-grained processor selection is repeated until a suitable processor is identified.
Since a convincing (I)IoT honeypot needs to expose authentic system behaviour and communicate with the outside world, the AutoHoney(I)IoT framework will provide: (i) a method to attach communication interfaces to the emulated embedded processor and bridge them to physical as well as simulated hardware, and (ii) a method to attach custom external peripheral device models to a communication interface whose behaviour can be scripted in a simple way.
The FFG funded project started in July 2019 and is expected to conclude in December 2021. It is jointly realised by SBA Research, FH Technikum Wien, TU Wien and Trustworks GmbH, all situated in Vienna, Austria.
Link:
[L1] https://kwz.me/hEt
References:
[1] K. Angrishi: “Turning Internet of Things(IoT) into Internet of Vulnerabilities (IoV): IoT Botnets”, arXiv Prepr. ArXiv1702.03681, 2017.
[2] A. Spognardi et al.: “Analysis of DDoS-Capable IoT Malwares”, in Proc. of INSERT, 2017.
[3] F. Bellard: “QEMU, a fast and portable dynamic translator”, USENIX Annual Technical Conference, FREENIX Track. Vol. 41. 2005.
Please contact:
Christian Kudera, Georg Merzdovnik, Edgar Weippl, SBA Research, Austria