by Florian Skopik, Markus Wurzenberger and Roman Fiedler (AIT Austrian Institute of Technology)
Today’s security solutions usually address only single architectural layers, and are unable to take account of the full picture. This leads to a system operator having only a limited view regarding the root cause of a cyberattack, which can reduce the overall availability of cyber-physical systems (CPS). Particularly for complex and stealthy multi-stage attacks, an approach is required that correlates information from all CPS layers, including the field area, the SCADA backend, the enterprise IT and the WAN (in the case of large-scale CPS) to promptly react to emerging malicious activities.
The degree of sophistication of modern cyber-attacks has increased in recent years, and in the future these attacks will increasingly target cyber-physical systems (CPS). Unfortunately, today’s security solutions that are used for enterprise IT infrastructures are not sufficient to protect CPS, which have largely different properties, involve heterogeneous technologies, and have an architecture that is very much shaped to specific physical processes. Furthermore, many best practice security techniques clash with the stringent safety requirements in CPS [1], e.g., weekly software updates might be acceptable in an enterprise IT environment, but certainly not in a safety-critical environment with certified equipment. The chances of unwanted side-effects are enormous. As a consequence, detective security techniques must be applied to CPS [2], which rely upon the ability to detect attacks in a timely and accurate manner.
Therefore, the objective of the project synERGY is to develop new methods, tools and processes for cross-layer anomaly detection (AD) to enable the early discovery of both cyber- and physical-attacks, which will have an impact on the security of CPS. To achieve this, synERGY develops a novel behaviour-based anomaly detection approach that leverages machine learning to understand a system’s normal behaviour by investigating network flows as well as events on endpoints reflected in log data, and detect consequences of security issues as deviations from the norm. While common anomaly detection concepts usually fail for enterprise environments, because of their complex behavioural patterns, these approaches are very promising for CPS that have a rather deterministic behaviour. The solution proposed by synERGY flexibly adapts itself to specific CPS layers (e.g., automatically applies more sensitive behaviour deviation thresholds to more deterministic system areas, and is less strict for other parts), thus improving its detection capabilities. Moreover, synERGY interfaces with various organisational data sources, such as asset databases, configuration management, and risk data (the latter is especially of interest for flexible monitoring of the most threatened components). The aim is to facilitate the semi-automatic interpretation of detected anomalies, which can help to reduce false positives and increase the utility of the system to an operator. The synERGY approach is evaluated in real smart grid vendor environments – a societally important CPS [3]. As a “by-product” of this evaluation, we plan to make raw CPS data sets available (in compliance with synERGY’s data management plan) to other research groups working on new anomaly detection methods. Because of the modular approach taken in the project, we propose that the synERGY results will be readily applicable to a wide range of CPS in value networks, and will thus result in broader impact on future CPS security solutions.
synERGY Technical Objectives
The main technical research goal of synERGY is to develop a novel anomaly detection system – based on cross-layer monitoring from embedded field devices to enterprise IT – which can be applied to a wide range of CPS operating in different application domains. The abstract concept with its four focus areas (FA) is depicted in Figure 1. This means that synERGY offers the ability to adapt the monitoring layer to specific CPS environments predefined by the combination of ICT infrastructure and physical/industrial processes of an organisation (FA I). Eventually, synERGY should have the capability to detect a priori unspecified errors, anomalies and misuse (for which no predefined signatures exist), e.g., potential consequences of security incidents, with more accuracy than existing products (FA II). Furthermore, synERGY supports the analysis and interpretation of detected anomalies using end-user specific organisational context, information from existing security mechanisms, such as firewalls, antivirus programs, IDSs, etc. and open/external information about threat intelligence, provided by mailing lists, vulnerability databases and online platforms (FA III). This is vital to assess a given security situation quicker and – in course of the organisational security processes (FA IV) – enable CPS providers to deploy counter measures earlier than with today’s solutions.
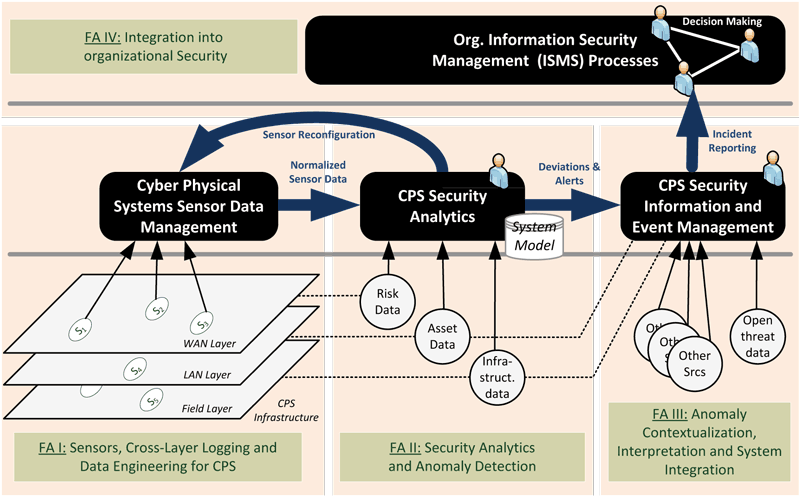
Figure 1: The synERGY concept and four main focus areas (FA).
The Project synERGY and its Consortium
In order to attain these ambitious goals and finally ensure the wide applicability of developed tools and procedures, the project consortium consists of a vital mix of academics with deep knowledge in cyber security (Austrian Institute of Technology, TU Wien, Universitaet Klagenfurt) and security solution vendors from the industry (Huemer iT-Solutions). In addition to the development of scientific methods, the proper demonstration of the applicability of synERGY’s results in a real-world environment is of paramount importance in order to test and evaluate the planned system. Thus, two electrical utility providers are involved as end users (Linz AG, Energie AG). Furthermore, the involvement of economic experts (MOOSMOAR Energies) and national stakeholders (Ministry of Defence) is essential to account for vital non-technical aspects and ensure the later adoption of synERGY in real application environments. synERGY is a 30-month national research project running from 2017 to 2019 and is funded by the Austrian FFG Research Program “ICT of the Future”.
Link:
https://synergy.ait.ac.at/
References:
[1] S.K. Khaitan and J.D.McCalley: “Design Techniques and Applications of Cyberphysical Systems: A Survey”, in Systems Journal, IEEE , vol.9, no.2, pp.350-365, June 2015.
[2] R. Mitchell and I.R. Chen: “A survey of intrusion detection techniques for cyberphysical systems”. ACM Comput. Surv. 46, 4, Article 55, 2014.
[3] F. Skopik and P. Smith: “Smart Grid Security – Innovative Solutions for a Modernized Grid”, Elsevier Science Publishing, 2015, ISBN: 978-0-12-802122-4.
Please contact:
Florian Skopik, AIT Austrian Institute of Technology,
Center for Digital Safety & Security, Austria
+43 664 8251495,











