by Gianfranco E. Modoni, Marco Sacco (ITIA-CNR) and Alberto Trombetta (University of Insubria)
In order to face the challenge of strengthening its cyber-security, a manufacturing company can follow the approach of aligning cybersecurity-related goals with its specific business objectives.
Cybersecurity represents one of the biggest challenges for modern manufacturing companies. At the same time as these companies are striving to take advantage of recent advances in ICT, they are also facing an increasing number of threats and vulnerabilities, which can jeopardise cybersecurity of their information systems. In particular, data confidentiality, integrity, and availability are at risk. Hence, it is essential to identify new security measures that mitigate the risk of internal and external attacks against the systems to an acceptable level, thus protecting the information processed by those systems. To this end, several high profile international organisations have been conducting various cybersecurity initiatives. One of the most relevant is the National Institute of Standards and Technology’s (NIST) “Framework for Improving Critical Infrastructure Cybersecurity” (CSF) [1], which provides guidance for any organisation to assess and manage cybersecurity risks.
However, a framework such as the CSF is only useful to a manufacturing company if its application is framed within the business context of the particular organisation. A process of alignment of the core activities provided by the NIST CSF with the business model could greatly help an organisation to analyse and assess their cybersecurity issues. A potential definition and workflow for this alignment, using an IDEF0 model, is represented in Figure 1. The input of the alignment activity is a virtual image of the factory, representing the evolution of its products, processes, and production systems [2]. The constraints of the alignment consist of a list of conditions that the company has to meet in order to be compliant with the CSF, while the configuration consists of a list of known threats and vulnerabilities that are widely acknowledged in the literature. The output of the alignment process is the cybersecurity posture of the company. The resulting output posture can then be compared with the target posture, thus highlighting the gap that needs to be filled for the organisation to reach compliance with the NIST CSF.
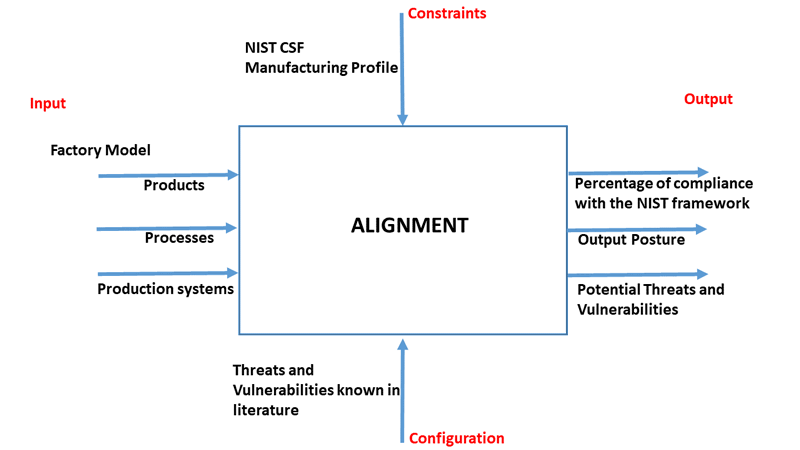
Figure 1: IDEF0 diagram for the alignment activity.
The current state of the art shows that cybersecurity information models are typically decoupled and separated from business process information models – an approach that fragments the efforts that an organisation is making to strengthen cybersecurity. We propose the introduction of a semantic-based data model to harmonise the involved information and overcome this fragmentation. This model overlaps and correlates core concepts provided by the NIST CSF with the business dynamics behind any given manufacturing company. In this way, it mediates and reconciles concepts of different knowledge domains (Figure 2), allowing the integration of cybersecurity within the context of an organisation’s business model. Thus, this approach can help the organisation to allocate investments towards specific objectives compliant with the NIST CSF. On top of this model, an ontology expressing complex relationships (and which will serve as basis for the reasoning tool) is defined using OWL; the ontology is then processed using SWRL rules that encode the set of conditions that the factory has to meet in order to comply with the NIST CSF. A good starting point for implementing the required conceptual models is the Enterprise Core Ontology [3], an existing model that represents the dynamics behind the factory world.
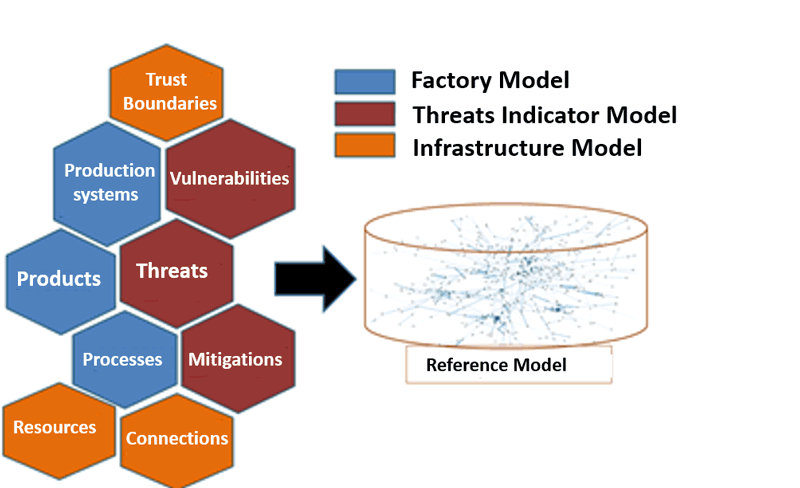
Figure 2: Reuse of existing reference models to implement the conceptual model.
Ongoing and future developments will address three main goals. First, an automated way to measure the compliance of a specific business scenario with CSF has to be conceived and developed, taking into account the model previously defined. Second, the proposed conceptual model will be used as pillar to design and develop a new software tool to support a company’s technicians to identify and manage cybersecurity priorities. Third, an empirical evaluation of the proposed approach in a real-world case study is needed, in order to test its correctness and effectiveness.
References:
[1] NIST: “Framework for Improving Critical Infrastructure Cybersecurity”, 2014.
[2] G. E. Modoni, et al.: “A telemetry-driven approach to simulate data-intensive manufacturing processes”. Procedia CIRP, 57, 281-285, 2016.
[3] G. E. Modoni, et al.: “Enhancing factory data integration through the development of an ontology: from the reference models reuse to the semantic conversion of the legacy models”, International Journal of Computer Integrated Manufacturing, Ed. Taylor & Francis, 2016.
Please contact:
Gianfranco E. Modoni, ITIA-CNR, Italy











