by Uwe Roth (Luxembourg Institute of Science and Technology, LIST)
The new EU General Data Protection Regulation (GDPR) [1][L1], which will come into effect in 2018, demands transparency as one of the main principles for the collection, processing, storing and transfer of personal data. Transparency ensures that individuals can enforce their legal rights: to withdraw consent for their personal data to be processed or to request that their data are erased. At the Luxembourg Institute of Science and Technology we filed a patent, based on blockchain technology, that guarantees transparency in the context of files that are exchanged in a shared data pool. It guarantees that access by partners to specific files can be traced without a central entity.
Closed consortia who provide and exchange personal data between their partners need to understand the impact that the new General Data Protection Regulation (GDPR) of the European Union will have on their processes. In fact, it demands that the data controller must provide to an individual, upon request, information about the transfer of their personal data to third parties, third countries or international organisations.
The legal counterpart and single point of contact for a person that provided their personal data will not be the consortium as a whole, but a single data controller partner who has collected the private data and published it in the data pool. This contractual partner needs to ensure that the processing of personal data is legal, and may be sued if it fails to fulfil its legal obligations.
In the absence of a central logging facility that acts as a trusted third party, and without sophisticated access to appropriate management solutions, it can be virtually impossible to trace which partner organisations have accessed individual data sets. It can, therefore, be extremely difficult to provide relevant information to an individual who requests that their data be deleted. As a consequence, the processing of personal data inside a consortium might, in the future, be criminalised or result in a fine.
In 2016, The Luxembourg Institute of Science and Technology, LIST [L2], filed a patent application that addresses these new demands with a solution based on the latest file-distribution, blockchain and encryption technologies. In a purely decentralised peer-to-peer environment of equal partners, without requiring any centralised instance or further authorisation steps, the solution empowers the provider of data to trace the access to the data by partners in the distributed and shared data pool. This trace of access is without any doubt and cannot be denied.
The solution is based on a file distribution network of encrypted files. It creates redundancy to increase availability and to improve download speed (Figure 1). The blockchain network is used to log the access to the files which will allow every access of the data by any partner in the network to be traced. In our solution, we abstract from the use of the underlying blockchain technology (Figure 2) in an ISO-OSI [2] layered way: Starting from the lowest blockchain-network layer that is only used to broadcast a number of bytes amongst the network, each new layer on top of this adds another level of complexity, e.g., adding point-to-point communication, adding end-to-end-encryption, or adding messaging. This allows us to make our approach independent from the specific blockchain implementation that is finally used, and replace it without the need to re-implement the entire solution.
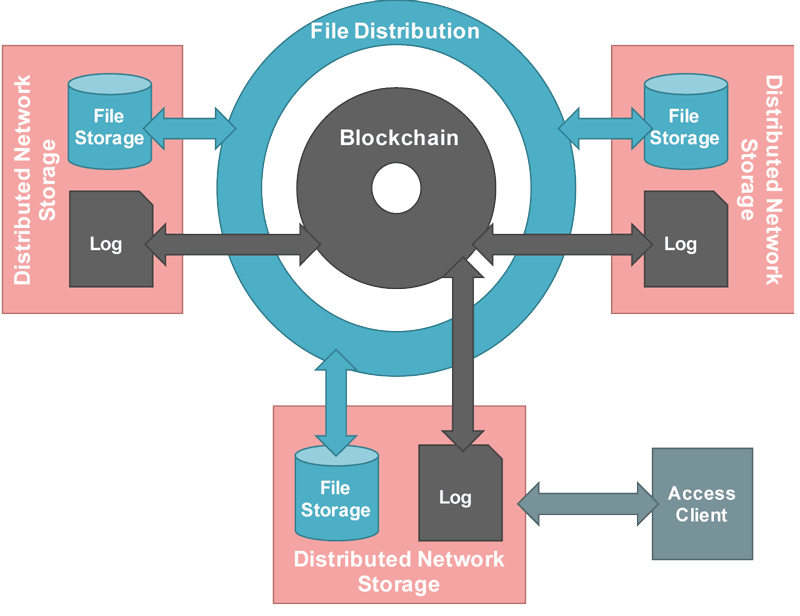
Figure 1: Clients access their local network storage that acts as a node in a decentralised peer-to-peer network.
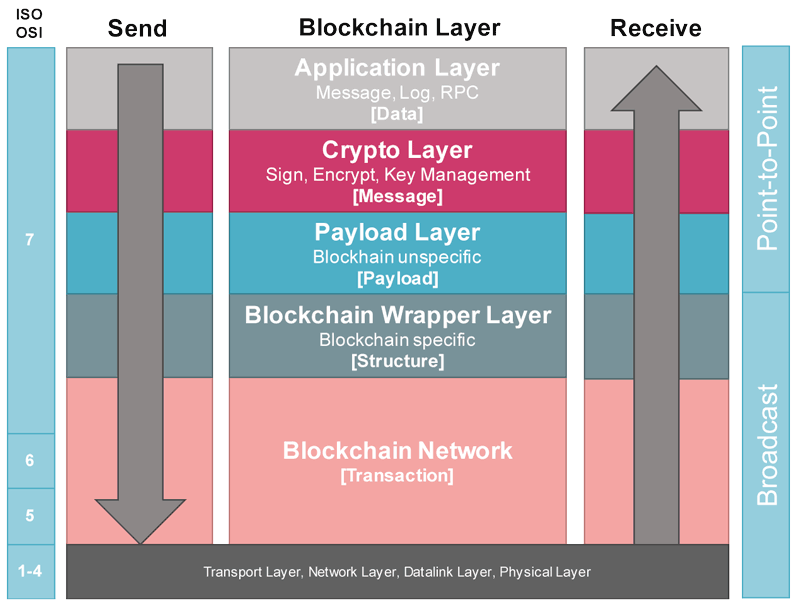
Figure 2: Usage of the blockchain in a layered architecture, in relation to the ISO-OSI model.
We are currently in the process of developing a first proof-of-concept that includes all the elements described in the patent, and, at the same time, searching for partners that can provide use-cases that are relevant for specific markets. For example, an clinical research consortium that exchanges genomics data between their partners, which may be international. An alternative use-case is the tracing of access, not only to personal data inside a shared data pool, but also to copyright protected data that triggers payment obligations. In addition to logging access to files, we are currently investigating an approach to log access to any type of service, including data inside a distributed database.
Links:
[L1] http://www.eugdpr.org
[L2] http://www.list.lu
References:
[1] GDPR, Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation), online: http://data.europa.eu/eli/reg/2016/679/oj
[2] H. Zimmermann: “OSI Reference Model – The ISO Model of Architecture for Open Systems Interconnection“, IEEE Transactions on Communications, vol. 28, no. 4, April 1980, pp. 425–432.
Please contact:
Uwe Roth
Luxembourg Institute of Science and Technology, LIST