by George Hatzivasilis (FORTH), Kostas Fysarakis (Sphynx) and Sotiris Ioannidis (FORTH)
Modern educational tools and computer technologies are now getting adapted in the cyber-ranges field. Simulation, emulation, as well as serious gaming, provide an enhanced training experience under realistic conditions and accurate operational environments. The THREAT-ARREST Horizon-2020 project is developing a model-driven platform for professional cyber-security training and the raising of awareness for individuals and organizations.
Nowadays, more-and-more cyber-security training is emerging as an essential process for the lifelong personnel education in organizations, especially for those which operate critical infrastructures [1], [2]. Gartner estimates that the global cyber-security awareness and training market will worth around $1.5 billion by 2021. This is due to security breaches on popular and widely-used services that become publicly known and raise the people’s security awareness [L1], [L2].
This study combines pedagogical practices and cyber-security modelling in an attempt to support dynamically adaptive training procedures [3]. The training programme is tailored to the trainee’s needs and technical capabilities, promoting the continuous monitoring and adaptation to his/hers performance. As the trainee accomplishes the basic evaluation tasks, the assessment starts involving more advanced features that demand higher level of understanding. The overall method is integrated in a modern cyber-ranges platform and three pilot applications on training programmes for smart energy, shipping, and healthcare employees are developed.
The THREAT-ARREST approach [L3] is composed of 4 main phases (see Figure 1): i) analysis, ii) programme establishment, iii) training and user feedback, and iv) post-training monitoring and security evaluation.
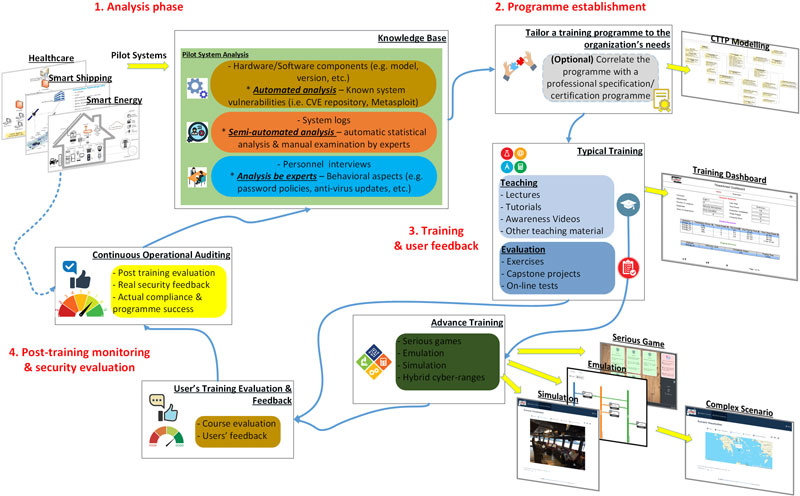
Figure 1: The THREAT-ARREST lifecycle.
At first, we analyze the customer organization system and establish the knowledge base for the training programme. The goal is to estimate the current security status and specify the weak points (e.g. system or behavioral vulnerabilities). The platform’s Assurance tool installs monitoring modules in the pilot system that capture its technical aspects (like the type and version of the running software of the installed hardware components) and check if it operates in a secure manner. Then, it searches to widely-known security repositories (i.e. CVE) and automatically discovers the active vulnerabilities of the system (e.g. if a server uses MSQL 5.5.35, then it is vulnerable to buffer overflow attacks based on the CVE-2014-0001). The vulnerabilities set is evaluated in a semi-automated fashion by the experts, who identify the most significant of them for the examined organization. Experts also interview the organizations personnel and record the followed operational procedures (e.g. password-update policy, anti-virus updates, etc.). The training programme is developed afterwards based on the overall outcomes of the initial analysis.
Also, during this phase, the experts collect real-operational log or other data files from the examined system. This knowledge is further processed in order to enhance the advance training procedures of the THREAT-ARREST platform. At first, we perform statistical analysis on the original data in order to disclose the statistical patterns of each file. This is performed either through manual examination by experts or via an automatic statistical analysis module. The goal is to produce synthetic events (i.e. a series with legitimate and/or phishing emails) or other data (i.e. a database’s content with dummy but realistic entries) via our Data Fabrication tool that will be later used in order to provide advance training under realistic conditions.
Then, based on these results we tailor a Cyber Threat and Training Preparation (CTTP) programme to the organization’s special needs, which could also be combined and cover the training for a professional certification programme (e.g. Certified Information Security Manager (CISM) by ISACA or Certified Information Systems Security Professional (CISSP) by ISC2), in order to increase the THREAT-ARREST’s efficiency. Afterwards, we collect the related teaching material for the typical training (e.g. lectures, tutorials, awareness videos, etc.) and model the advance training scenarios based on emulation, simulation, and serious gaming.
Once the trainee has completed the basic training for a learning unit, the accompanied CTTP models are activated in the Dashboard and the trainee can now proceed with the advanced training. The CTTP models describe a virtual system and how to instantiate it via the Emulation, Simulation, and Gamification tools.
These virtual labs and digital twins, which could resemble the organization’s actual system and followed procedures, offer hands-on experience to the trainees/personnel. Thus, they can test and evaluate new policies and technologies, break-down the system, restore the default state and start over again, without affecting the real system. The trainees start the programme, consume the teaching material and are evaluated against the desired learning goals.
After the completion of the training, the platform displays the results for each trainee and the programme as a whole. This process indicates the scores of the trained personnel and their achievements regarding the educational procedures. Finally, the trainees can also complete questionnaires and provide feedback to the THREAT-ARREST operator, e.g. for the platform modules, the programme, etc., in order to update and improve our system. All these form ordinary features of training platforms.
However, the successful completion of a programme does not always reflect to the improvement of the pilot organization’s security in a straightforward manner [1]. The security level can be increased only if the trainees apply what they have learnt in the actual system. The evaluation of this phase is one of the THREAT-ARREST’s novelties in contrast to other competitive solutions [2].
Thus, our platform continues to audit the pilot system for a determined period after the training phases. The deployed controls from the initial phase continuously assure the organizations security-sensitive components. The goal is to capture if the trainees really applied what they were toughed.
For example, in the analysis phases we discover that the trainees do not update their email passwords in a regular basis, i.e. by examining the log-file of the mailing server. Thus, we tailor a programme to include the learning topic of password management. When the programme is finished, we inspect the servers log and check if the password-update entries have been increased or not.
The confirmation that the personnel adheres with the learned features, and thus the system’s security is really improved, constitutes the actual evaluation that the programme was successful. Feedback is gathered from this phase in order to improve the THREAT-ARREST’s operation for future training iterations and new programmes.
Links:
[L1] https://www.eda.europa.eu/info-hub/press-centre/latest-news/2018/09/13/cyber-ranges-federation-project-reaches-new-milestone
[L2] https://www.concordia-h2020.eu/
[L3] https://www.threat-arrest.eu/
References:
[1] Urias et al.: “Cyber Range Infrastructure Limitations and Needs of Tomorrow: A Position Paper,” ICCST, IEEE, 2018.
[2] Schwab et al.: “Cybersecurity Experimentation at Program Scale: Guidelines and Principles for Future Testbeds,” EuroS&PW, IEEE, 2019.
[3] Sultatos et al.: “The THREAT-ARREST Cyber-Security Training Platform,” ESORICS – MSTEC workshop, Springer, 2019.
Please contact:
George Hatzivasilis
FORTH-ICS, Greece