by Juan Caballero
At the core of most cybercrime operations is the attacker's ability to install malware on Internet-connected computers without the owner's informed consent. The goal of the MALICIA project is to study the crucial role of malware in cybercrime and the rise in recent years of an “underground economy” associated with malware and the subversion of Internet-connected computers.
Cybercrime, criminal activity conducted via computers connected to the Internet, is a growing threat for developed regions like Europe where nearly three quarters of households and a large number of the infrastructures are connected to the Internet, and an increasingly number of services and transactions happen online.
At the core of most cybercrime operations is the attacker's ability to install malicious programs (ie malware) on Internet-connected computers without the owner's informed consent. Malware includes bots, viruses, trojans, rootkits, fake software, and spyware. Malware enables attackers to establish a permanent presence in the compromised computer and to leverage it for their cybercrime operations. The target of these operations may be the compromised computers themselves eg stealing an organization's intellectual property or a user's banking credentials, or third parties. In the latter case, the compromised computers are simply assets, which the attacker employs to launch malicious activities such as sending spam, launching denial-of-service (DoS) attacks, faking user clicks on online advertisements (ie click-fraud), or simply as a stepping stone to hide its location.
The goal of the MALICIA project at the IMDEA Software Institute is to study the crucial role of malware in cybercrime and the recent rise of a far-reaching “underground economy” associated with malware and the subversion of Internet-connected computers. Gone are the days where attackers compromised computers and built malware to show off their skills to peers. These days, the malware ecosystem revolves around cybercrime and the monetization of compromised computers.
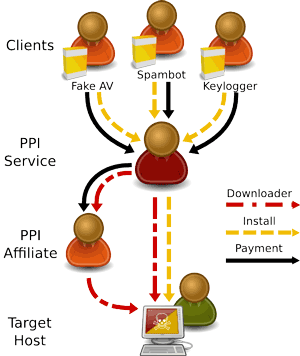
Figure 1: The Pay-Per-Install market
As the malware ecosystem has grown larger and more profitable, specialization has come to the marketplace. Attackers have understood that tackling the entire value-chain from malware creation to monetization poses a daunting task requiring highly developed skills and resources. As a result, specialized services have been created at all stages in the malware-monetization chain, such as toolkits to automate the construction of malware, program encryption tools to evade antivirus (AV) software, “bullet-proof” hosting, and forums for buying and selling ill-gotten gains. Specialized services lower the barrier to entering the malware ecosystem. However, defenders can also take advantage of specialization since disrupting the specialized services disrupts the different malware operations using them.
As a first step in the MALICIA project, we have collaborated with researchers at the University of California, Berkeley and the International Computer Science Institute to investigate the commoditization of malware distribution in the form of pay-per-install (PPI) services. PPI services offer criminals a simple way to outsource the distribution of their malware. The clients provide their malware to the PPI service and select the number of desired installations (called installs) in each geographical area. The PPI service takes care of installing the malware on compromised computers in exchange for a small fee that ranges from $180 for a thousand computers in some European countries and the US, down to $7 for a thousand computers in Asia.
To satisfy the clients' demand for installs, the PPI provider typically outsources malware distribution to third parties called affiliates. PPI providers pay affiliates for each compromised computer, acting as a middle man that sells installs to the clients while buying installs from affiliates. Each affiliate may specialize in some specific malware distribution method (eg bundling malware with a benign program and distributing the bundle via file-sharing networks; exploiting web browsers through drive-by-downloads; or social engineering). The PPI service gives each affiliate a downloader program customized with a unique affiliate identifier. When the affiliate installs the downloader in a compromised computer, the downloader connects back to the PPI service to download the client programs. After installing the client programs on the compromised host, the downloader reports the affiliate identifier and the affiliate is credited with an install.
To understand the PPI market we infiltrated four PPI services. For this, we developed infrastructure enabling us to (1) interact with PPI services by mimicking the protocol interactions they expect to receive from affiliates, and (2) collect and classify the malware being distributed by the PPI services. Using this infrastructure we harvested over a million malware programs and classified them by malware family as well as monetization methods. Our analysis revealed that of the world's top 20 malware families, 12 employed PPI services for their distribution. It also revealed that some malware families exclusively target the US and a variety of European countries. The monetization methods in use are varied including: spam, installing fake antivirus software, information-stealing, denial-of-service, click-fraud, and adware.
Much remains to be learnt about the malware ecosystem and the specialized economy supporting cybercrime. Our current work strives on deepening our understanding of other parts of the ecosystem. One overarching goal is evolving malware analysis from understanding what a malware program does, to also cover why it does it, ie what role the malware program plays in the cybercrime operation where it is used.
References/Link:
"Measuring Pay-per-Install: The Commoditization of Malware Distribution", J.Caballero, C. Grier, C.Kreibich, and V. Paxson. In Proc. of the 20th USENIX Security Symposium, San Francisco, CA, August 2011.
"Most Malware Tied to 'Pay-Per-Install' Market", B. Krebs, MIT Technology Review, Thursday, June 9, 2011. http://www.technologyreview.com/news/424241/most-malware-tied-to-pay-per-install-market/
Please contact:
Juan Caballero, IMDEA Software Institute, Spain
E-mail:










