by Jim Clarke
Europe's research framework programmes are committed to the establishment of a solid security and dependability infrastructure. The IST-SecurIST project has been charged with the preparation of a European strategic research agenda in the field of ICT for Security and Dependability, for the upcoming 7th research framework programme.
The Internet and other digital networks have now become an integral part of our economy and society. But as we are rapidly adopting more information and communication technologies (ICT) in services and commerce, private information is at increasing risk and security and dependability problems become prevalent. Indeed, today people are becoming more and more concerned about the increasing complexity of information and communication systems and the proliferation of privacy-invasive information gathering sources and techniques. In their online daily interactions, they often find themselves faced with high-profile losses of their personal information and with viruses, spam, phishing and other crimes of growing severity and sophistication. As a result, they find themselves in an undesirable situation in which they must put ever more trust into environments in which there is little or no way of understanding or assessing them properly.
To build an information society that will deliver growth and prosperity, we need to tailor ICTs to business and social needs, and ensure that they become useful tools for economic and social innovation. The starting point for making them useful is to foster trust and safeguard security in a networked world. In this respect, Europe's research framework programmes are committed to the establishment of a solid security and dependability infrastructure. The IST-SecurIST project (an IST Co-ordination Action) has been charged with the preparation of a European strategic research agenda in the field of ICT for Security and Dependability, for the upcoming 7th research framework programme (FP7, 2007-2013). In order to achieve this objective, the SecurIST project has established two fundamental bodies: the European Security and Dependability Task Force (STF), and the SecurIST Advisory Board.
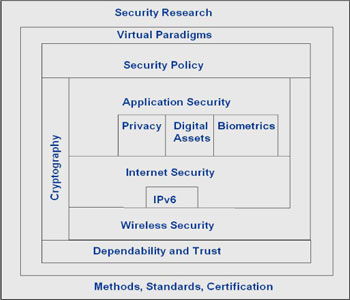
The STF is currently comprised of 180 members spread across thirteen fundamental thematic areas (initiatives) of research. It provides a forum for consolidation and consensus building. The thematic initiatives are shown in the figure, which provides a visual interpretation of how these initiatives are integrated and work together.
The SecurIST Advisory Board is composed of European experts in information security and dependability. The charter of the board is to oversee, review, enhance and promote results from the STF (see http://www.securitytaskforce.eu).
Recently, based on inputs from the STF, the SecurIST Advisory Board has issued a document presenting its recommendations for a future security and dependability research framework in Europe, for the period 2007-2013. Under the headline From 'Security and Dependability by Central Command and Control' to 'Security and Dependability by Empowerment', the Advisory Board is recommending the following nine key research areas:
- Empowerment of the stakeholders: Stakeholders of the information society include individual citizens, industry and academia, non-governmental organisations and governments. Empowerment of the stakeholder is vital as there is a clear technological trend towards decentralization of technology, as well as of its management and control. Respon-sibility, authority and control have to move more towards the end user.
- Europe-specific security and dependability: Europe has a very specific heterogeneous culture and history and set of attitudes to trust and society that requires specific research profiling.
- Infrastructure robustness and availability: Further research efforts are needed for the assurance of ICT network and service infrastructures, as well as the robustness and availability of critical infrastructure, such as health, energy, transport or finance.
- Interoperability: Research on the interoperability between security and dependability technologies and standards.
- Processes for developing secure and dependable systems: Research on the systematic improvement of secure and dependable system development (including hardware and software) from their design phase.
- Security and dependability preservation: In an increasingly complex world of evolving requirements, technologies and systems, maintenance of effective system security and dependability is critical and is essential for preserving user confidence.
- User-centric security and dependability standardisation: Strengthen the structured involvement of end users and their respective representatives into relevant standardization activities involving security and dependability technologies.
- Security and dependability of service oriented architectures (SOA): The need to establish and maintain trust and manage policy regulations and service level agreements in an SOA context, together with commensurate advances in software engineering to deliver service expectations.
- Technologies for security: Research is needed to provide a higher assurance of trusted communication and handling of digital information. Cryptology and trusted functionality and computing need to be considered.
In addition to these nine key research areas, four future grand challenges covering a 10-20 year vision are presented by the Advisory Board. They illustrate possible longer-term possibilities and implications:
- Countering vulnerabilities and threats within digital urbanization: This challenge addresses open problems that we will face in security and dependability from the expansion and globalization of digital convergence by 2010-2015.
- Duality between digital privacy and collective security: digital dignity and sovereignty: This challenge deals with future privacy issues of all the stakeholders, whether citizens, groups, enterprises or states. It addresses the problem of how to override the 'Big Brother' syndrome and 'dark security', ie, the future assurance of digital sovereignty and dignity for the various stakeholders.
- Objective and automated processes: This challenge addresses the problem of how to attain a controllable and manageable world of complex digital artefacts by 2015 and how to inject regular, quantitative techniques and engineering to make the field truly scientific.
- Beyond the horizon: a new convergence: This last challenge deals with the preparation of a new convergence at a horizon of 2020 and beyond, which is the bio-nano-info-quantum 'galaxy' and the new security and dependability challenges that will emerge.
Links:
The full report of the SecurIST Advisory Board recommendations:
http://www.securitytaskforce.eu/
Please contact:
Jim Clarke, Waterford Institute of Technology, Telecommunications Software and Systems Group, SecurISTCoordinator
E-mail: jclarke![]() tssg.org
tssg.org