by Juan Ramón Troncoso-Pastoriza and Elsa Prieto Pérez
The WITDOM project (empoWering prIvacy and securiTy in non-trusteD environments) develops innovative technical solutions for secure and privacy-preserving processing of genomic and financial data in untrusted environments.
The advent of outsourced and distributed processing environments like the Cloud is prompting fundamental transformations in whole ICT ecosystems, while bringing new opportunities to stakeholders in terms of the availability and rational use of physical resources with large-scale savings in IT investments. Conversely, it also poses new security challenges, especially for ensuring robust protection of privacy and integrity of personal information, which are essential for societal acceptance of new ICT schemes, services and solutions.
In this context, the WITDOM project focuses on developing innovative solutions for truly efficient and practical privacy enhancing techniques and efficient signal and data processing in the encrypted domain for outsourced environments. WITDOM’s main goal is to produce a framework for end-to-end protection of data in untrusted environments, with a particular focus on data-outsourcing scenarios where new threats, vulnerabilities and risks due to new uses require end-to-end security solutions that will withstand progress for the lifetime of applications they support.
WITDOM aims to develop three main innovations in this area. Firstly, a novel framework for end-to-end security and privacy that will guarantee efficient and verifiable provision of privacy in the context of ICT services owned by third-party providers of distributed processing and storage. This framework will maximize independence from stated security and privacy commitments by respective providers, and minimize the current need for blind trust from clients, based solely on written consents. The initial contribution of this framework builds upon a requirements elicitation methodology, synergizing the results of the recently ended FP7 project PRIPARE with a co-design process to fuse privacy into the first stages of the systems design process, materializing a true Privacy-by-Design methodology.
The second dimension of innovations deals with the actual design and development of tools and technologies for efficient privacy protection of data outsourced and processed in untrusted environments. These techniques can be categorized according to the four main research areas addressed in WITDOM: efficient lattice cryptosystems for homomorphic processing, allowing for faster and more resource-efficient encrypted-domain processing [1]; accurate and effective secure signal processing to cope with the marriage between cryptography and the ubiquitous signal processing operations when dealing with sensitive signals [2]; efficient privacy-enhancing technologies for obfuscation, noise addition, anonymization and data masking, measuring and achieving quantitative guarantees that the processed data will be unidentifiable and the produced results unlinkable; and last, but not least, efficient and scalable integrity and consistency verification techniques to preserve fork-linearizability on data accessed and modified by several users on outsourced data stores [3]. The main strength in our approach is that these innovations are not applied independently or autonomously, but in an end-to-end secure and private architecture that defines a platform that can deploy privacy-preserving services on outsourced data with quantifiable and assessable technological guarantees. Promising initial results have already been produced within WITDOM’s roadmap, which will continue to advance the state of the art in these fields for the next two years.
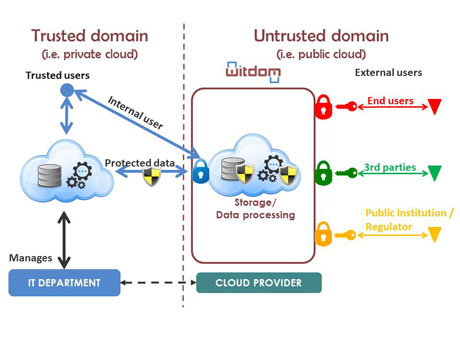
Figure 1: WITDOM generic architecture.
Finally, the third dimension of WITDOM’s innovations deals with the instantiation of the developed framework, platform and tools in two carefully chosen use-case scenarios, for which privacy is essential owing to the sensitivity of the involved data, and where privacy and confidentiality constraints are a true barrier to using outsourced architectures and Cloud-based deployments. The first use-case is a health scenario that involves outsourcing genetic data processes and workflows for large research analyses and individual clinical analyses; genetic data is extremely sensitive, and genomic privacy has become a hot topic for research and innovation, to which WITDOM contributes by focusing on solutions for outsourced processing of genetic data. The second scenario deals with outsourced financial analyses based on the management of both customers’ data and finance data, to enable credit risk calculations and card transaction fraud detection deployed as outsourced secure financial services over private and public Cloud environments.
Research and innovation in this field cannot ignore the impact of data protection regulations and directives on the evolution of Cloud-related environments and in the processing of personal and sensitive data. Therefore, WITDOM innovations are built upon a legal assessment and validation of the evolving European Data Protection Regulation, linking legal and ethical requirements with technological means to guarantee their enforcement.
The WITDOM project is a Research and Innovation Action funded by the European Commission’s Horizon 2020 programme and the Swiss State Secretariat for Education, Research and Innovation. This project, started in January 2015, joins together a multidisciplinary consortium comprising Universities, research centres, strong industrial stakeholders, and end-users: Atos(Spain) as the project coordinator, the University of Vigo (Spain) as the technical coordinator, Katholieke Universiteit of Leuven (Belgium), IBM Research (Switzerland), Fondazione Centro San Raffaele (Italy), BBVA (Spain), Gradiant (Spain), and the Ospedale San Raffaele (Italy).
Links:
http://witdom.eu/
https://twitter.com/W1TD0M
https://www.linkedin.com/grp/home?gid=8257514
References:
[1] D.D. Chen et al.: “High-Speed Polynomial Multiplication Architecture for Ring-LWE and SHE Cryptosystems”, IEEE Trans. on Circuits and Systems 62-I(1): 157-166 (2015).
[2] J. R. Troncoso-Pastoriza and F. Pérez-González: “Secure Signal Processing in the Cloud: enabling technologies for privacy-preserving multimedia cloud processing”, IEEE Signal Process. Mag. 30(2): 29-41 (2013).
[3] M. Brandenburger, C. Cachin and N. Knežević: “Don't trust the cloud, verify: integrity and consistency for cloud object stores”, ACM SYSTOR 2015: 16:1-16:11.
Please contact:
Juan Ramón Troncoso-Pastoriza
University of Vigo
E-mail:











