by Darío Ruiz López
The RERUM framework is designed to be both secure and private, whilst maintaining the open nature of the Internet of Things (IoT) by empowering users by allowing them to define dynamic access criteria based on user reputation.
One of the main obstacles currently hindering the adoption of IoT is the lack of trust in the security and privacy provided by IoT frameworks. By offering a framework designed to be both secure and private, RERUM aims to foster the adoption of IoT, specifically in the scope of Smart Cities.
However, there is a very serious issue when trying to apply the Privacy by Design (PbD) techniques to the IoT [1]: A common perception of the IoT is that its sole purpose is to connect everything to the Internet, but the IoT is more than this: the IoT will allow devices connected to the IoT to connect to each other for any purpose, including purposes that we cannot foresee. Hence, IoT is conceptually aiming to achieve an open world. This is one of the biggest strengths of the IoT because it potentially offers an almost infinite world of data to data mining engines. At the same time, however, it makes it incompatible with the Privacy by Design concept.
In contrast to the openness of the IoT, in Privacy by Design, access to data is meant to be granted only to those people or applications previously agreed to by the owner of the data, and only for purposes stipulated by the owner [2]. That is, Privacy by Design conceptually aims at a closed world by default, rendering it necessary to define in advance who can access the data and for what purpose.
Moreover, even if the user wanted to grant access to any IoT device in the world and for any purpose (as is intended by the IoT), there is no way this could be achieved, since the user would have no way to know in advance who will be wanting to access the data and, even worse, the purpose of this access may not even exist yet, since the concept of IoT implies new purposes may appear with time as new devices and applications are developed.
Thus, there exists a dilemma between fully supporting IoT and PbD that makes it necessary to come to a compromise between them. Though RERUM has mainly opted for PbD, it has also studied the nature of this dilemma and tried to reduce it by analyzing the objectives of both the IoT and PbD with the goal of attaining as many objectives as possible - even if this means adapting the way the concepts were written.
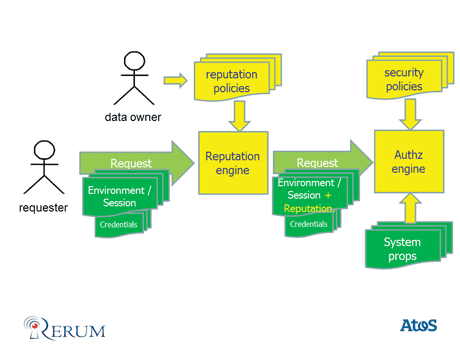
Figure 1: RERUM approach to reduce the IoT-PbD dilemma.
IoT is not about violating privacy, but providing technical means for devices to connect to each other throughout the internet, and PbD is not about impeding connectivity, but empowering users to control how their data are used. Hence, the way to approach IoT and PbD should be to find ways to let users grant access to their data to IoT devices while maintaining control of how this access is granted. However, since the nature of IoT means that the number of consumers and purposes of the requests is near to infinite, this control must be accompanied by automatic processing that allows the access decision to be made based on criteria defined by the user. In this way we allow the user to define access criteria that will let IoT devices access data according to those criteria, even for unknown applications and devices, and even for unknown purposes.
RERUM proposes a reputation engine configurable with rules defined by the user to enrich the authorization process with the result of this evaluation, so the data owner has the option of defining access criteria that allow data access by unknown users, even for unknown purposes if the data owner wishes.
The RERUM project is a research project subsidized by the European Commission through the Seventh Framework Programme. RERUM aims to create an IoT framework for Smart Cities based on the concepts of Security and Privacy by Design.
RERUM started its work in September 2013 and is currently being executed by the RERUM consortium, formed by the following companies and institutions throughout the European Union: Eurescom, Atos, Siemens, Zolertia, Forth, Cyta, the universities of Bristol, Linköping and Passau, and the municipalities of Heraklion and Tarragona.
References:
[1] J. Höller, et al.: “From Machine-to-Machine to the Internet of Things: Introduction to a New Age of Intelligence”, Elsevier, 2014, ISBN 978-0-12-407684-6.
[2] Regulation of the European Parliament on the protection of individuals with regard to the processing of personal data and on the free movement of such data. 2012 European Commission (http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=COM:2012:0011:FIN:EN:PDF)
Please contact:
Darío Ruiz López, Atos, Spain
E-mail:











