by Gabriele Lenzini, Johan Muskens and Andrew Tokmakoff
As part of the EU-ITEA research programme, Trust4All project partners from industry, research institutes and universities teamed up to design and develop an embedded systems framework that helps component-based applications to maintain a high level of dependability and security. Philips research and the Dutch Telematica Instituut designed and developed the framework's trustworthiness management features.
Component-based Software Engineering is an emerging development paradigm that promises to accelerate software development and to reduce costs by assembling systems from pre-fabricated software components. It has also been adopted for the development of software for embedded devices.
There are several trends in component-based embedded devices. First, systems are becoming more open in the sense that more third party components (ie, software components that have not been developed by the device vendor) are used for their development. So, component-based devices run various components that interact with each other to provide the high-level system functionalities. Furthermore, systems are becoming more dynamic in the sense that the software configuration of a device changes when the device is owned and used by the end user. These trends enable an increasing number of features to be offered by embedded devices, but threaten the devices' dependability and security properties. In the context of an open component-based system that supports unmanaged upgrading and extension (changing the software configuration), it is possible that component-based devices may host unstable components that could negatively affect the devices' dependability. Here, the most risky scenario is the download of new components to extend the system's capabilities; this exposes the system's internals to potentially malicious components that may compromise the system's overall security.
Recent research indicates that the use of Trust Management can be a useful tool when addressing the dependability and security concerns encountered in distributed and embedded systems.
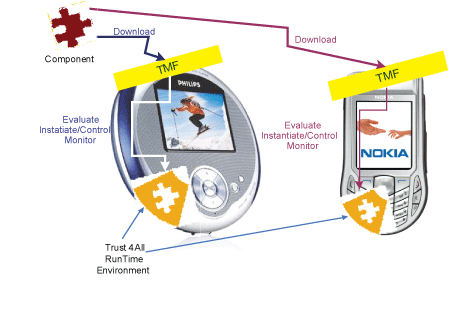
The Trust4All project has embraced this emerging topic and investigated its application in the context of component-based embedded systems. Our approach has been to extend the component-based middleware, first developed within the EU-ITEA Robocop and Space4U projects, to include a Trustworthiness Management Framework (TMF), as shown in the figure. This framework provides low-level mechanisms that can be used to control and enforce components' behaviour, based upon established Trustor-Trustee relationship. The goal of TMF is to support easy and late (possibly runtime) integration of components and still have dependability and security properties that are satisfactory to the user.
The TMF design addresses the following challenges:
-
The TMF acts on behalf of Trustors and explicitly takes their trust requirements into account.
-
The TMF makes use of 'metric sources' to monitor and report on the system's overall behaviour.
-
The TMF makes use of 'actuators' to control a Trustee's mode of operation, thereby influencing the system's behavioural characteristics.
-
The TMF makes use of the Space4U Resource Management Framework to decide whether a component's requested mode of operation should be allowed from a resource consumption point of view.
A core part of the TMF is the Trustworthiness Evaluation Function (TEF), which is responsible for calculating the trustworthiness of a component/Trustee. It can be parameterised with Trustor-specific dependability and security requirements. By analysing a Trustee's 'estimated quality attributes' and recommendations, the TEF can evaluate a component's 'present trustworthiness' (or compliance) in terms of the degree to which it satisfies the Trustor's stated dependability and security requirements. Through analysis of component's behaviour, the TEF calculates (utilising Subjective Logic) the 'believed trustworthiness' of a component in terms of the following aspects:
-
Benignity: the belief that the component will continue to satisfy the Trustor's requirements,
-
Stability: the belief that the Trustee's behavioural qualities of will remain within a given neighbourhood.
The triple of compliance, benignity, and stability is used to make control decisions that regulate the system's overall dependability and security characteristics. For example, when a component with positive compliance begins to show a reducing benignity, the TMF may decide to 'wrap' the component in an attempt to minimise its potential impact on the system, since it is displaying increasingly less-compliant behaviour. Similarly, when there is a strong disbelief in stability, this may indicate a need to re-evaluate the component's estimated quality attributes and, as a consequence, re-evaluate its compliance.
The project began in July 2005 and will run for two years. Its efforts are now moving from research and design towards implementation and construction of demonstrators in the domains of consumer electronics, mobile devices, and domotics.
Many companies and researchers collaborate in Trust4All: CWI, Océ-Technologies, Philips Research (project coordinator), Telematica Instituut, Eindhoven University of Technology (TU/e), Univ. Leiden (the Netherlands). Nokia, Solid Information Technologies, VTT (Finland), ESI, FAGOR, IKERLAN-Electrónica, Robotiker, and Visual Tools (Spain).
Links:
http://www.research.philips.com
http://www.telin.nl
http://www.win.tue.nl/trust4all
Please contact:
Gabriele Lenzini, Telematica Instituut, The Netherlands
Tel: + 31 53 4850463
E-mail: Gabriele.Lenzini![]() telin.nl
telin.nl
Johan Muskens, Philips Research Europe, The Netherlands
Tel: + 31 40 2742491
E-mail: Johan.Muskens![]() philips.com
philips.com